Create Authentication Policy
Configure an MCP policy to secure your MCP Server with authentication and authorization.
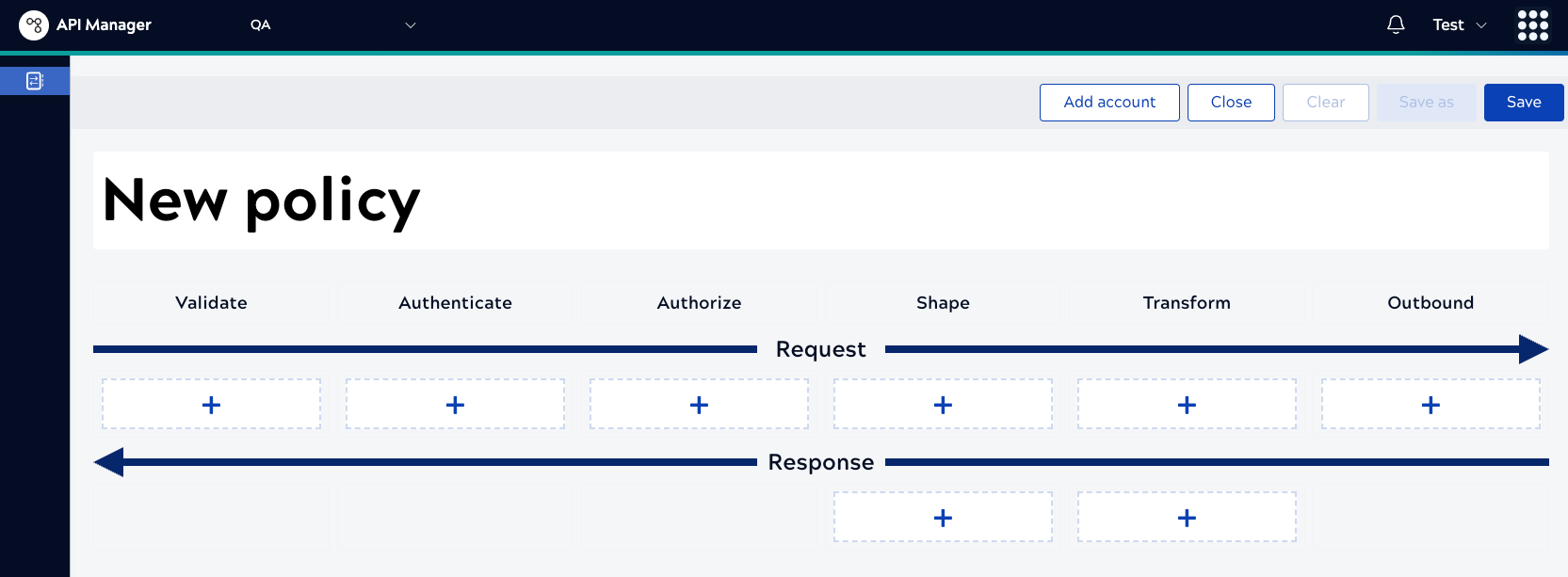
MCP Servers use policies for authentication. MCP uses the same policy builder that APIM 3.0 does. The policy builder contains a suite of authentication, authorization, validation, traffic shaping, and transformation rules. These rules compose the policy. You can use existing rules or policies created for APIM Services or create new ones specifically for MCP. This topic covers creating policies for MCP Server authentication.
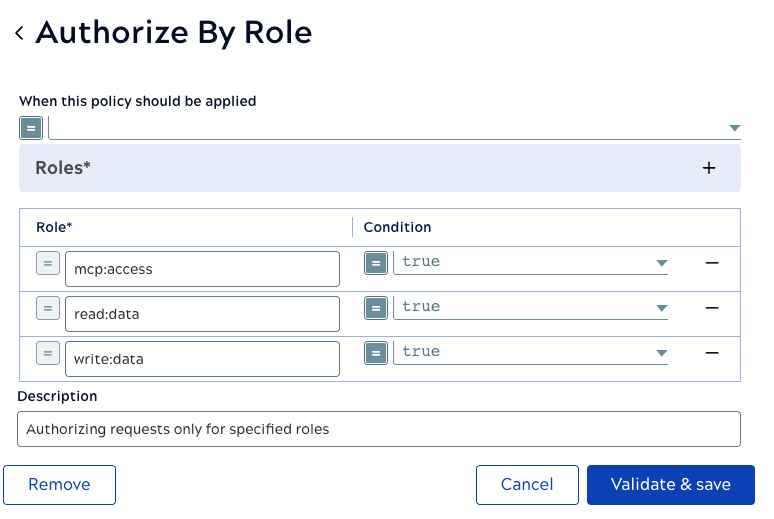
Available authentication methods for MCP:
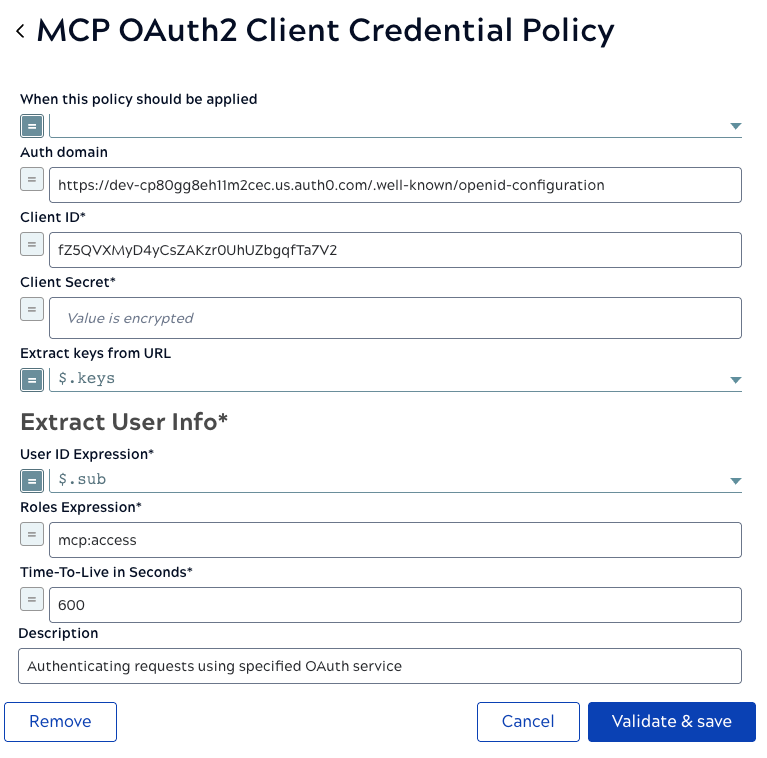
- MCP OAuth2 Client Credentials Policy: For application-to-application authentication
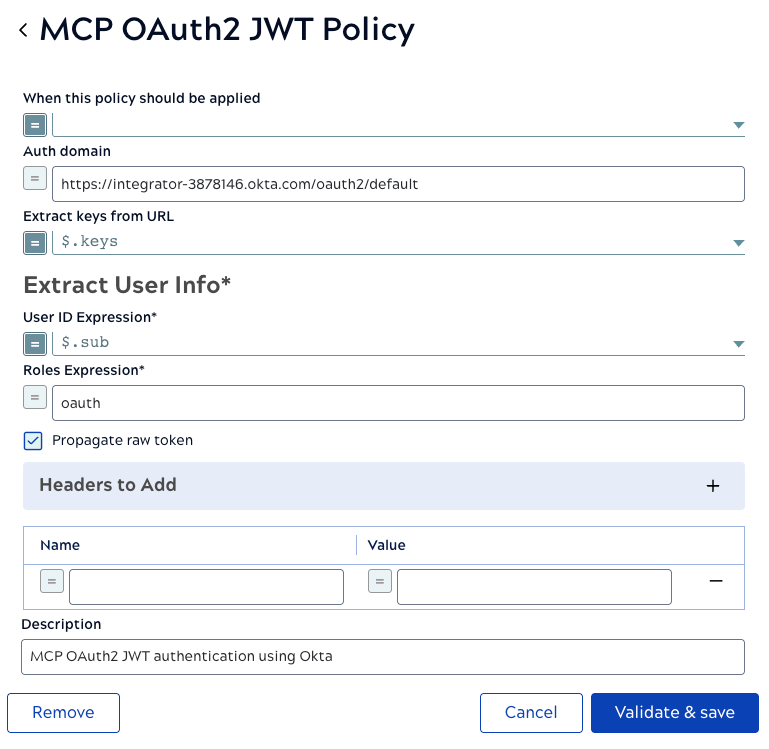
- MCP OAuth2 JWT Validator Policy: For validating JWT tokens from identity providers
- API Key Authenticator: Simple token-based authentication
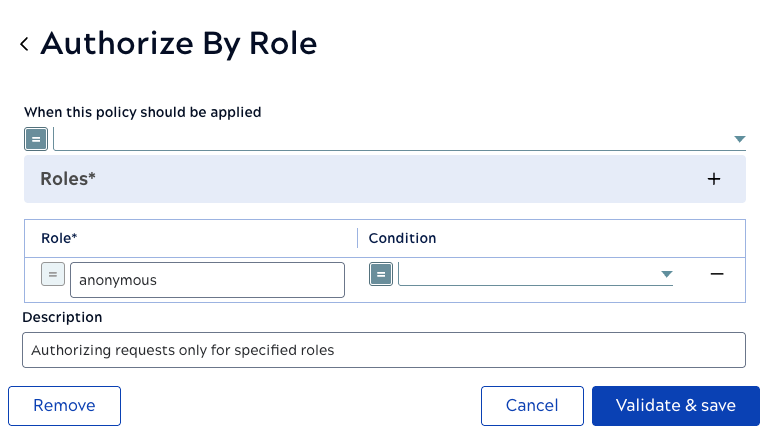
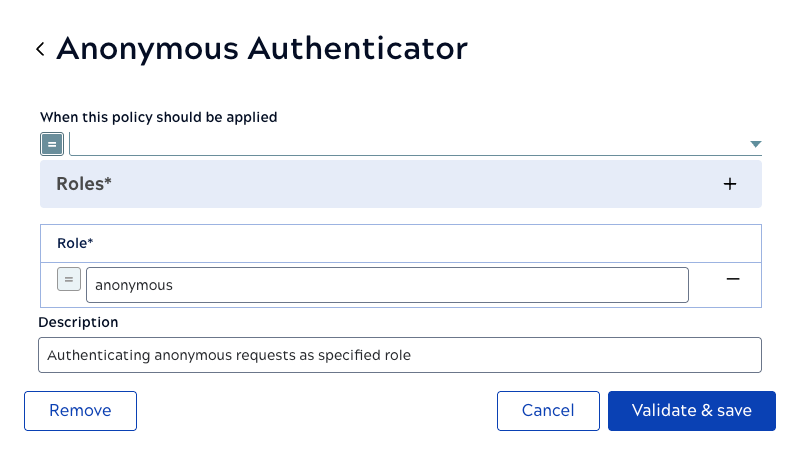
- Anonymous Authenticator: No authentication (development only)
-
Open the Policy Catalog.
-
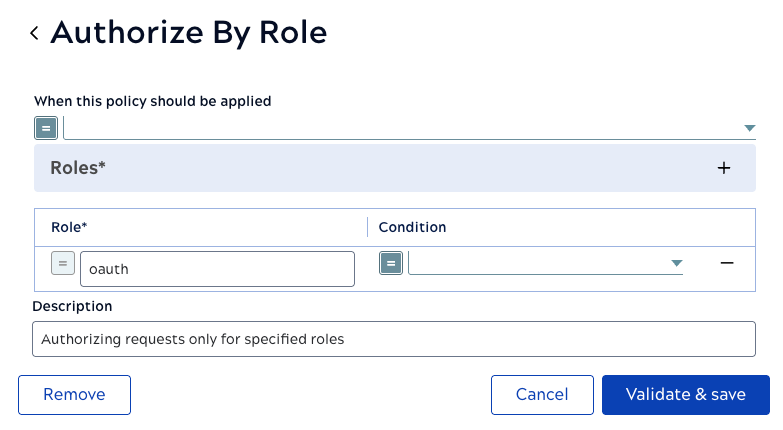
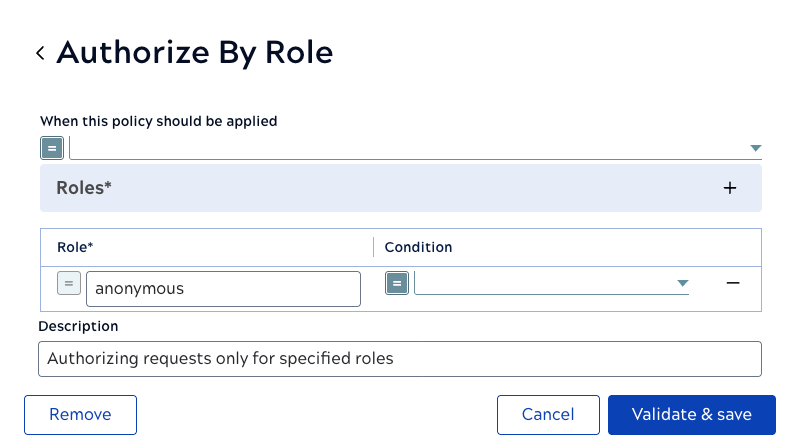
Add Rules.
-
Configure MCP Policy using OAuth2 Client Credentials
-
Configure an MCP Policy to generate a JSON Web Token for Authentication
-
Configure an MCP Policy for Anonymous Authentication
-
Save the Policy.
Your authentication policy is now created and can be selected when configuring MCP Servers.
After creating the policy, return to Register MCP Server to select this policy for your MCP Server.