Introduction to Policies
A Policy is a collection of rules that apply to specific Services or endpoints. A Catalog Policy applies to all Services unless overridden at the Service or endpoint level. You can create one Catalog Policy. Each rule in the Catalog Policy has a checkbox that determines whether the Catalog rule overrides the same type of rule set at the Service or endpoint level. With the Always use Catalog rule box:
- Unchecked: Rules set at the Service and endpoint override the Catalog Policy rule.
- Checked: The Catalog Policy rule overrides any Service or endpoint Policies that contain the same rule.
Take the example of an IP restriction rule with different values at the Catalog, Service, and endpoint levels. Unless the Always use Catalog rule box is checked for that rule in the Catalog Policy, the endpoint rule applies.
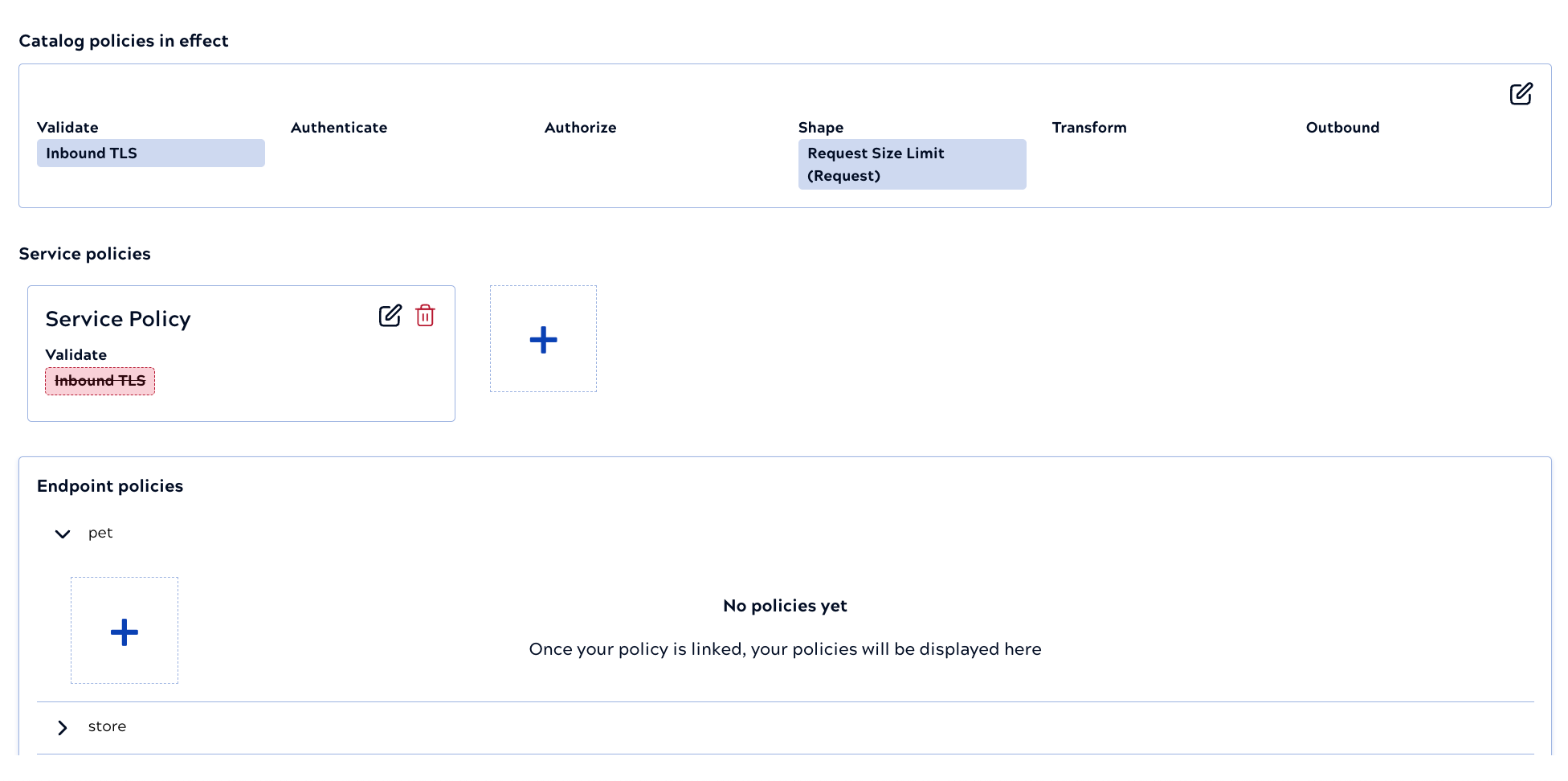
The Policies tab shows rules that take precedence in a blue box and any that would be overridden in a red box. In the following example, the Always use Catalog rule box is checked for the Inbound TLS rule:
Create Policies from the Policy Catalog:
- Click the Catalog Policy entry to create or modify the Policy that applies to all Services in the catalog.
- Click New Policy to add a new Policy that you can later associate with a Service or endpoint.
Both actions open the Policy builder:
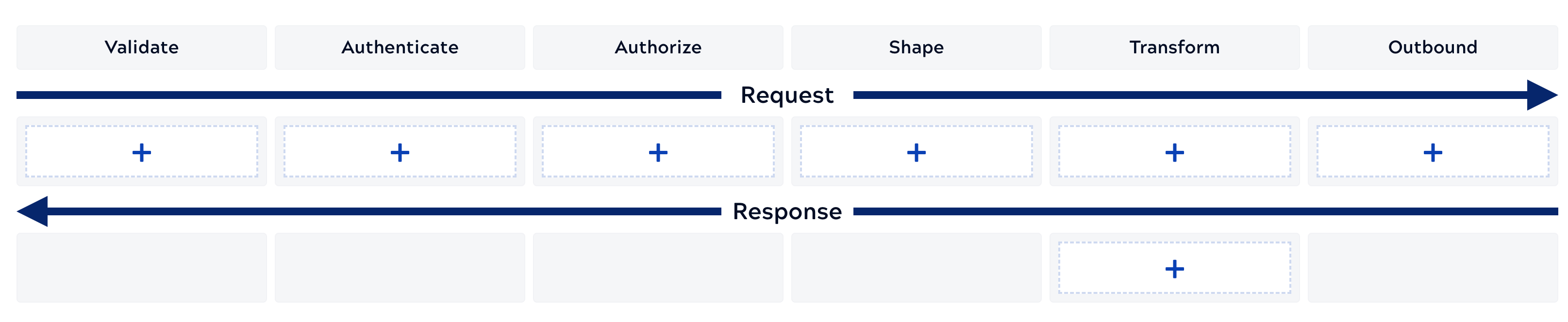
The Policy builder categorizes rules by their type and shows the general order in which they apply during the request and response. For example, authentication and authorization follow validation. There are some exceptions, such as request transformation, retries, and client throttling, that don't strictly execute in the order in which they appear.
The first five request rule categories apply to all requests. The outbound category only applies to requests to external endpoints as described in Request execution flow. The following describe the available rules by category and provide some common use cases:


