Splunk Writer
Overview
You can use this Snap to write data to a specific Splunk index.
- This is a Write-type Snap.
Works in Ultra Tasks
Prerequisites
None.
Limitations and known issues
None.
Snap views
| Type | Description | Examples of upstream and downstream Snaps |
|---|---|---|
| Input | It must contain one or more binary data objects. | |
| Output | A document with {"status": "success"} if the upload is successful. |
|
| Learn more about Error handling. | ||
Snap settings
- Expression icon (
): Allows using JavaScript syntax to access SnapLogic Expressions to set field values dynamically (if enabled). If disabled, you can provide a static value. Learn more.
- SnapGPT (
): Generates SnapLogic Expressions based on natural language using SnapGPT. Learn more.
- Suggestion icon (
): Populates a list of values dynamically based on your Snap configuration. You can select only one attribute at a time using the icon. Type into the field if it supports a comma-separated list of values.
- Upload
 : Uploads files. Learn more.
: Uploads files. Learn more.
| Field/Field set | Type | Description |
|---|---|---|
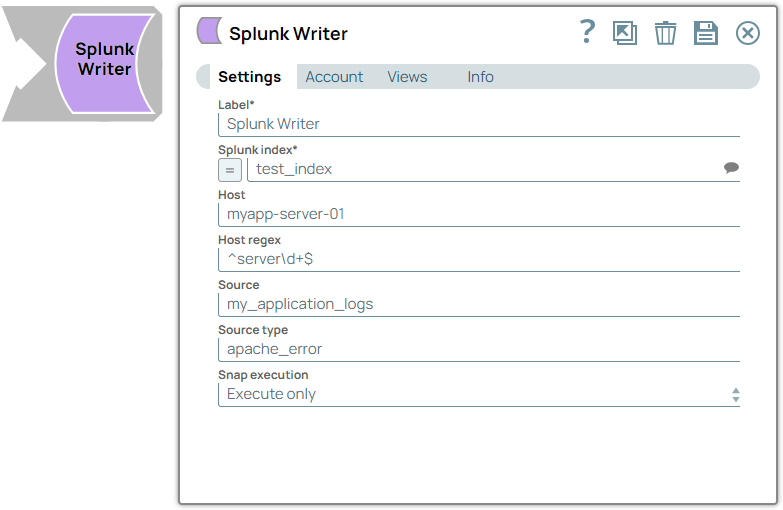
| Label | String |
Required. Specify a unique name for the Snap. Modify this to be more appropriate, especially if more than one of the same Snaps is in the pipeline. Default value: Splunk Writer Example: Employees list |
| Splunk index | String/Expression |
Required. A repository for data in Splunk Enterprise. When Splunk Enterprise indexes raw event data, it transforms the data into searchable events. You may select one from the suggested list. If the "=" button is pressed, it can be an expression evaluated with pipeline parameters. Default value: N/A Example:
|
| Host | String/Expression |
Specify the host argument of the event. For more information refer to Splexicon: Host, and host. Default value: N/A Example: myapp-server-01 |
| Host regex | String/Expression |
Specify the host_regex argument of the event. For more information refer to host_regex. Default value: N/A Example: "your_regular_expression" |
| Source | String/Expression |
Specify the source field for the incoming data, indicating the origin or location of the log events being sent to Splunk. For more information refer to Splexicon: Source. Default value: N/A Example: my_application_logs |
| Source type | String/Expression |
Specify the sourcetype field for the incoming data, indicating the format or category of the log events being sent to Splunk. For more information refer to Source type and Splexicon: Source type. Default value: N/A Example: apache:access |
| Snap execution | Dropdown list | Choose one of the three modes in which the Snap executes. Available options
are:
|


