Configure GitHub Enterprise Server and the Git Integration
Configure GitHub Enterprise Server and the SnapLogic Git Integration.
The SnapLogic Git Integration supports the on-premises GitHub Enterprise Server (GHES) with the app gateway and use of a Groundplex. The control plane communicates through the app gateway, which routes Git requests through a Groundplex to the Git Provider.
Prerequisites
To enable use of GHES with the Git Integration:
- In GHES, a GHES administrator:
- Creates a GitHub app for SnapLogic.
- Creates one or more repositories to store SnapLogic assets.
- In the SnapLogic environment, an Environment admin:
- Configures the Git Integration.
- Configures the Groundplex with the app gateway.
Create the GitHub App
- A subscription to the Git Integration for GHES.
- GHES administrator permissions.
- Create a GitHub App to register SnapLogic with GHES.
- Follow the GitHub instructions to create a new GitHub App.
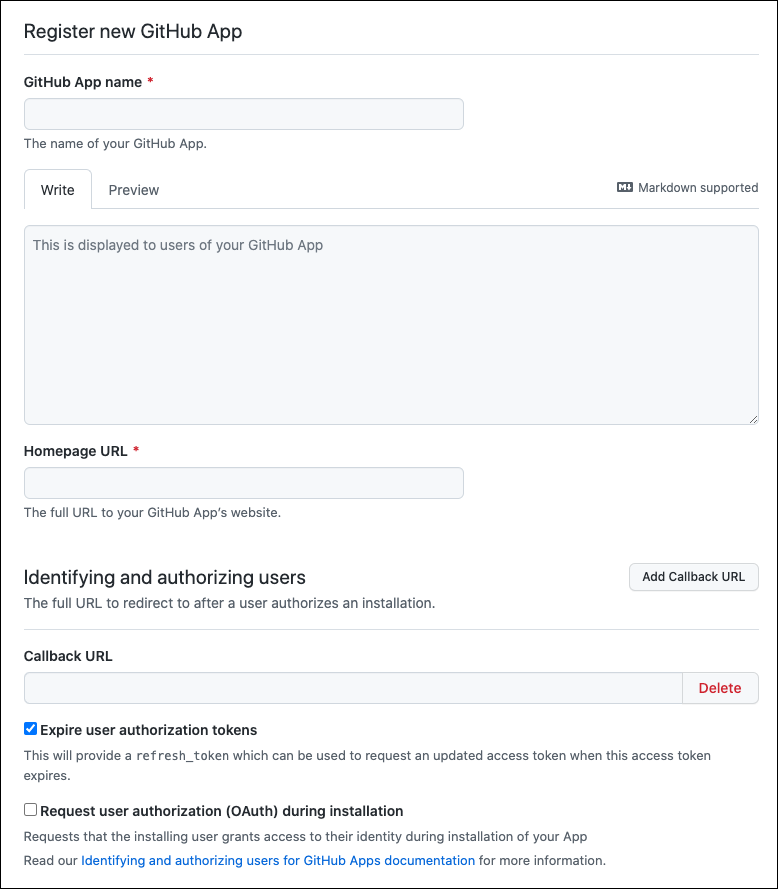
Field Description GitHub App name The name of your GitHub App. Example:
snaplogic-appHomepage URL The full URL to the GitHub app’s website. Users install the app from this page. Example:
https://your-GHES-server-URL/github-apps/snaplogic-app/Callback URL The full URL to redirect to after the installation is authorized. Example:
https://elastic.snaplogic.com/api/1/rest/asset/app/oauthcallbackExpire user authorization tokens Enable this option. - Contents: Read & write
- Deployments: Read & write
- Issues: Read & write
- Pull Requests: Read & write
Where can this GitHub App be installed Any Account - Save the App ID, which is required for SnapLogic configuration.
- Install the newly created GitHub App for the appropriate GHES organization.
- Use the buttons on the About page of the GitHub App to
generate and save a client secret and a private key.
The generated private keys are automatically downloaded in a .pem file.
- Follow the GitHub instructions to create a new GitHub App.
- Follow the steps in the GitHub documentation to limit repository visibility to the repositories for SnapLogic assets.
- Configure the network with the following settings:
Destination: SnapLogic Manager - Configure Git dialog Source: GHES GitHub App creation Client ID Available from the GitHub App. Client Secret Generated in the About page of the GitHub App. GHES URL Homepage URL App ID GitHub App name Private Key Generated in the About page of the GitHub App. The private key is stored in a .pem file that is automatically downloaded.
Configure the Git Integration in Admin Manager:
- In Admin Manager, go to .
- In the Git Integration page, set Git integration
type as Github Enterprise Server, and fill in the
settings.
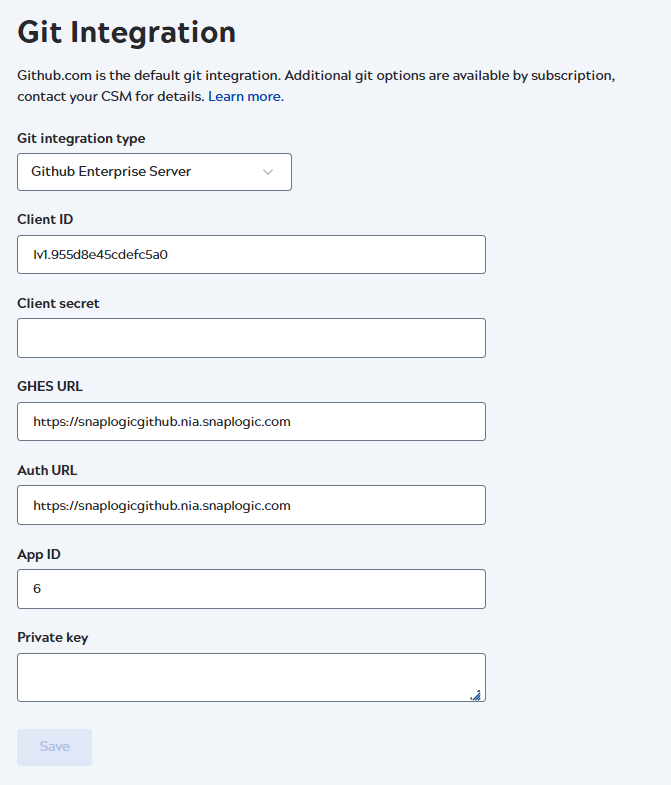
Field/Field set Description Client ID The value stored in the GitHub App. Client secret The field displays this value until you save the configuration, then it is hidden. Later, the only way to change it is to replace it. GHES URL The gateway URL used for the secure connection between your Groundplex and on-premises GHES machine. org-location-environment-appname.controlportname:port
Use the following segments to build in the GHES URL in the order listed:
- org: Org name without hyphens (-). For example:
myenterprise-snap-testshould be passed asmyenterprisesnaptest. - location: location of your groundplex. Always
sidekick. - environment: the value in the Environment field in the Snaplex Settings tab.
- appname:
github - controlplanename: the value for the control plane
your Org connects to:
- Production - Global:
appgateway.prod.snaplogic.io:8095 - Production - EMEA:
appgateway.emea.snaplogic.io:8095 - UAT:
appgateway.uat.snaplogic.io:8095
- Production - Global:
For example, with an environment (Org) named
testand a Groundplex with an Environment value ofdev, the GHES URL for self-managed GitHub would be as follows:http://test-sidekick-dev-github.appgateway.prod.snaplogic.io:8095
If your environment values have any special characters or spaces, then the characters must be removed when specifying the gateway URL string.
For example: With an environment (Org) named as
http://test12-sidekick-dev12-github.appgateway.prod.snaplogic.io:8095test-12with Environment value ofdev-12on the Global control plane, the gateway URL would be as follows:Attention: The original values on the Org and Environment can be retained. This change is only required for the GHES URL string.Auth URL The public Homepage URL used in the GitHub App creation. Important: This field now takes the Homepage URL, which formerly was used as the GHES URL.App ID The GitHub App installation ID Private key Copy and paste the RSA key from the .pem file generated during the GitHub App creation. - org: Org name without hyphens (-). For example:
- Click Save.
Configure your Groundplex for the App Gateway
Before you begin- Ensure that the Groundplex is in the same network as your GHES host.
- Log in to the environment (Org) configured for integration with the GHES.
- In Admin Manager, click the target Snaplex to open the Update Snaplex screen.
- Click the Node properties tab.
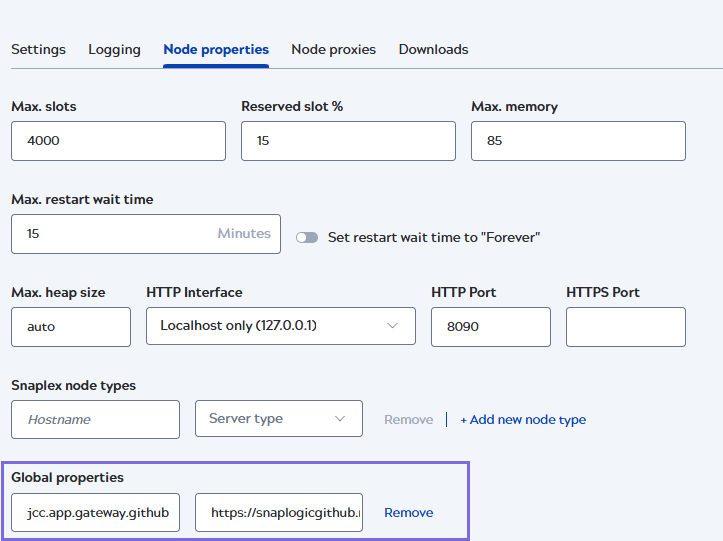
- Under Global properties, click +Add new node
type to add the gateway key-value pair. Attention: The Node properties must be configured on only one designated Snaplex and should exist only on the Snaplex configured for Git integration. In multi-Snaplex environments, configuring these properties on multiple Snaplexes can lead to intermittent GitHub runtime failures.
- Enter the information about the app gateway.
- Key:
jcc.app.gateway.github -
Value: The GHES URL for self-managed GitHub.
Example: https://snaplogicgithub.nia.snaplogic.com
- Key:
- Click Save.


